Late one evening, a startup founder checks server logs after a sudden slowdown. Buried among thousands of entries, one line keeps repeating: 185.63.263.20. At first glance, it looks like just another technical detail, the kind engineers scroll past without thinking. But as patterns emerge—unexpected traffic spikes, failed login attempts, unexplained latency—that single IP address starts to tell a much larger story.
In today’s internet-driven economy, numbers like 185.63.263.20 are not just strings of digits. They are signals. For entrepreneurs, tech readers, and founders, understanding what an IP address represents can mean the difference between blind reaction and informed strategy. This article explores 185.63.263.20 not as a mystery to decode for its own sake, but as a lens through which we can understand infrastructure, security, and trust in the digital world.
Understanding 185.63.263.20 in Plain Terms
At its core, 185.63.263.20 is an IPv4 address, part of the numerical system that allows devices on the internet to find and communicate with each other. Every request you make—opening a website, sending data to a server, loading an app—relies on IP addresses working quietly in the background.
What makes addresses like 185.63.263.20 interesting is not the number itself, but its context. IP addresses can be associated with hosting providers, data centers, corporate networks, or sometimes automated systems that generate large volumes of traffic. When founders or IT teams notice repeated interactions from a specific IP, it often raises practical questions: Is this traffic legitimate? Is it beneficial, neutral, or potentially harmful?
Understanding an IP address does not mean invading privacy or playing detective. It means reading technical signals responsibly and using them to make smarter operational decisions.
Why 185.63.263.20 Might Appear in Your Logs
There are many reasons why 185.63.263.20 could show up repeatedly in analytics dashboards or server logs. In many cases, it may simply belong to a hosting service or shared infrastructure used by multiple websites or applications. Modern cloud environments often route traffic through a limited range of IPs, which can make a single address appear more prominent than it really is.
For tech founders, the key insight is pattern recognition. One isolated request from 185.63.263.20 means very little. Thousands of similar requests within minutes might signal automated behavior. That automation could be harmless, such as search engine indexing or uptime monitoring, or it could indicate scraping, brute-force attempts, or misconfigured systems.
The IP address itself does not carry intent. The surrounding behavior—timing, frequency, endpoints accessed—is what gives it meaning.
The Business Relevance of Monitoring IP Addresses
From a business perspective, tracking addresses like 185.63.263.20 is less about paranoia and more about resilience. Entrepreneurs building digital products often focus heavily on features and growth, while infrastructure quietly supports everything in the background. When something goes wrong, IP-level visibility becomes crucial.
For example, unusual traffic from a single IP can inflate analytics, distort conversion metrics, or consume server resources. In e-commerce or SaaS environments, this can translate into slower response times for real users, increased hosting costs, or even service outages.
On the flip side, recognizing trusted IP addresses can help teams whitelist partners, integrate external services more smoothly, and reduce unnecessary security friction. In this way, IP awareness becomes part of operational maturity rather than just a security concern.
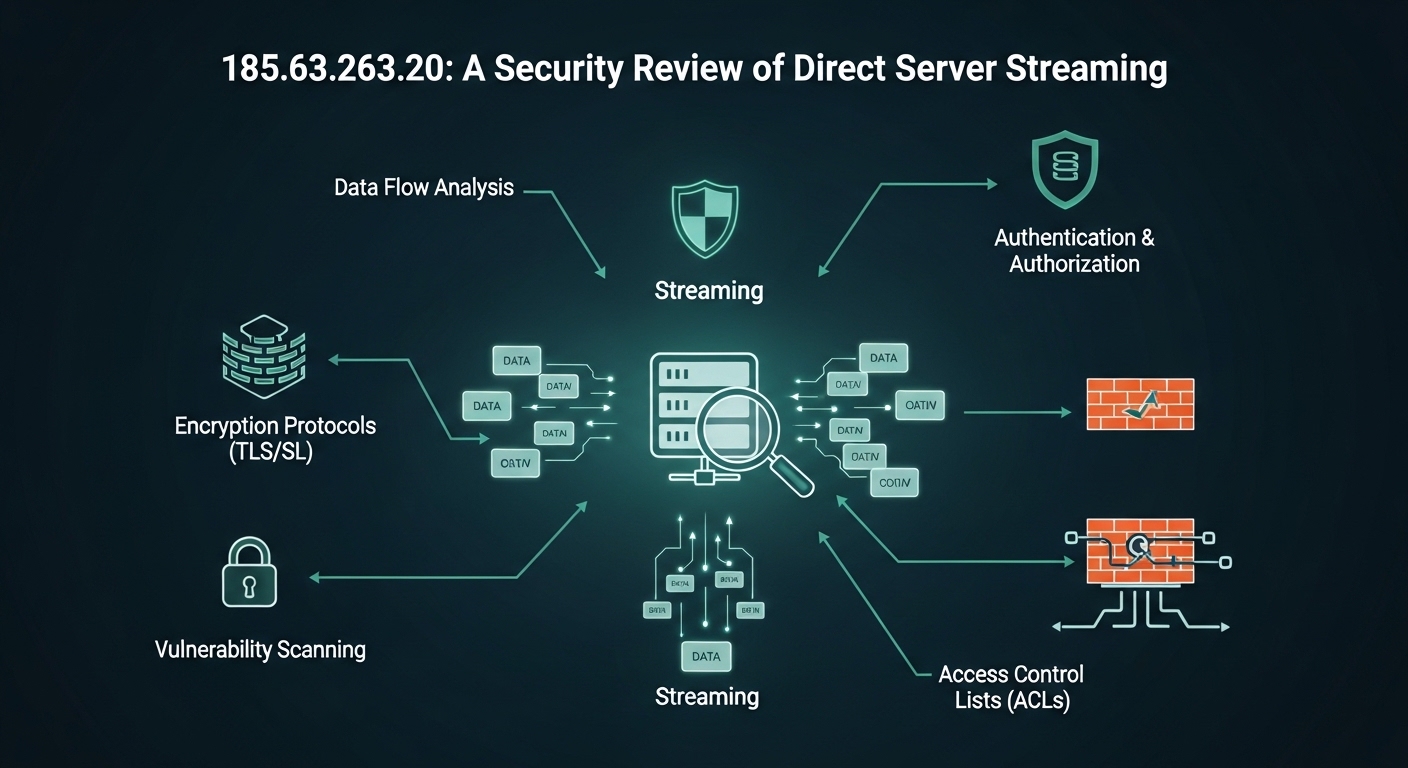
Security Implications of 185.63.263.20
Security conversations often become abstract, filled with acronyms and worst-case scenarios. Looking at a concrete example like 185.63.263.20 brings the discussion back to reality. When security teams flag an IP, they are not judging the number itself; they are responding to behavior patterns.
Repeated failed authentication attempts, rapid-fire requests to sensitive endpoints, or access attempts outside normal usage hours can all raise red flags. In such cases, temporarily rate-limiting or blocking an IP address can be a reasonable defensive step.
However, experienced teams avoid knee-jerk reactions. IP addresses can be reassigned, shared, or routed through proxies. Blocking 185.63.263.20 without sufficient context could disrupt legitimate users or third-party services. The real skill lies in balancing caution with evidence-based decision-making.
How IP Analysis Fits into Modern Infrastructure
Modern infrastructure has evolved far beyond simple server-client models. Cloud platforms, content delivery networks, and distributed systems mean that traffic often passes through multiple layers before reaching its destination. An address like 185.63.263.20 might represent an edge node, a proxy, or a shared resource rather than a single end user.
For founders and tech leaders, this complexity underscores an important point: IP addresses are clues, not conclusions. Effective infrastructure monitoring combines IP analysis with application logs, behavioral analytics, and contextual data.
This integrated view allows teams to distinguish between normal background noise and genuinely abnormal activity, reducing both false alarms and overlooked risks.
A Practical Table: What IP Signals Can Indicate
To ground the discussion, the table below shows how repeated appearances of an IP address such as 185.63.263.20 might be interpreted in different scenarios:
| Observation Pattern | Possible Meaning | Recommended Response |
|---|---|---|
| Low-volume, consistent requests | Monitoring or indexing activity | Allow and monitor |
| High-frequency requests to public pages | Scraping or automation | Rate-limit if needed |
| Repeated failed logins | Credential stuffing attempt | Temporarily block and investigate |
| Traffic spikes during off-hours | Automated scripts or bots | Analyze behavior before action |
This table is not a rulebook but a framework. Context always matters more than raw numbers.
Ethical and Legal Considerations
When discussing IP addresses like 185.63.263.20, it is important to acknowledge ethical boundaries. IP analysis should never drift into invasive tracking or misuse of data. Regulations and best practices emphasize proportionality and transparency, especially when user data is involved.
For businesses, this means using IP information strictly for operational security, performance optimization, and compliance. It also means documenting decisions and ensuring that automated blocks or filters do not unfairly impact legitimate users.
Responsible use of IP data builds trust—not just with customers, but within teams that rely on clear, ethical standards.
What Founders Should Actually Do
The most important takeaway for founders is not to memorize what 185.63.263.20 represents today, but to build systems that can interpret such signals tomorrow. This includes setting sensible alert thresholds, reviewing logs regularly, and encouraging collaboration between development, operations, and security teams.
Instead of reacting emotionally to unfamiliar IP addresses, mature organizations ask calm, structured questions. What behavior triggered attention? Has this pattern appeared before? What is the potential impact of acting—or not acting—on this information?
By approaching IP analysis as part of a broader decision-making process, founders turn technical noise into strategic insight.
Conclusion
In isolation, 185.63.263.20 is just a number. In context, it is a reminder of how much of the digital world runs on quiet, unseen interactions. For entrepreneurs and tech leaders, learning to read these signals is not about becoming paranoid or overly technical. It is about developing awareness.
IP addresses reflect the invisible flows of data that power modern businesses. When understood thoughtfully, they help teams protect users, optimize performance, and make confident decisions. The real value lies not in the address itself, but in the clarity gained by knowing how to interpret what it represents.